The Three AWS Web Application Firewall Managed Rules You Need to Deploy Now
A mind-boggling number of applications reside in the cloud without any protection. No web app firewall. No identity or access control. Nothing. They're just out there, open to attack.
That’s a nightmare for business, and a dream come true for attackers.
It’s also unwise given the increasing attention paid to applications as targets. Whether it’s to find a path into rich sources of data or to leverage the app as a distribution point for other nefarious purposes, application attacks are on the rise.
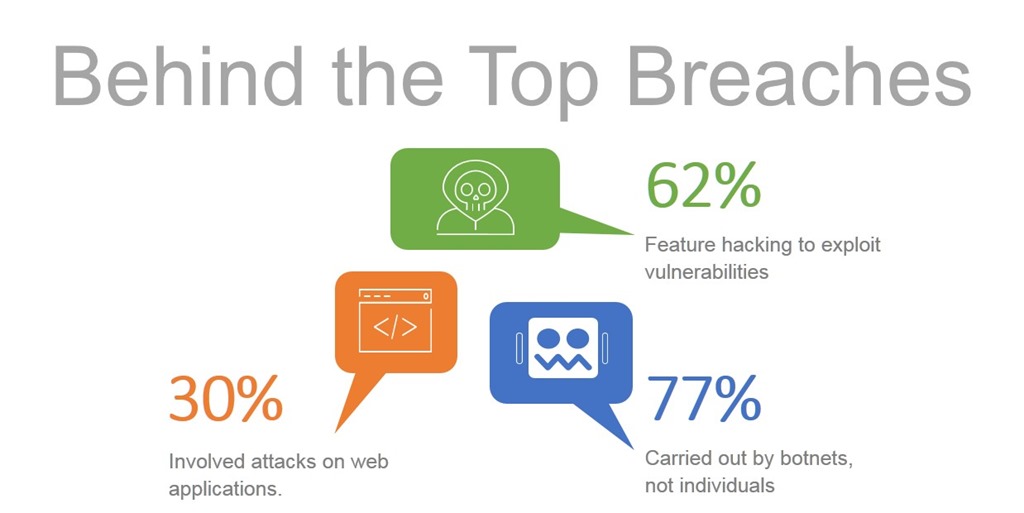
In fact, if we examine the top breaches we find that 30% involved attacks on web applications. A significant 62% featured hacking to exploit a vulnerability. And a staggering 77% were carried out by botnets – not individuals.
Which means you need to protect your apps from bots and vulnerabilities lest you become just another statistic.
And when I say your apps, I mean all your apps. All apps are critical apps when it comes to security – even in the cloud. Perhaps moreso in the cloud where apps might be deployed without even the rudimentary protections afforded by a network firewall.
But we can’t (and shouldn’t) ignore that complexity – especially of security solutions – can sometimes get in the way of protecting applications in the cloud. Just over one-third (34%) of respondents in our State of Application Delivery 2018 survey told us that “increasing complexity of security solutions” was a top security challenge for the coming year.
Security can be hard. But it doesn’t have to be; especially in the cloud.
Web App Security in the Cloud
For those unaware, AWS provides a pretty sweet platform for not just you to deploy your apps but for vendors to add functionality to it as well. In the security space, its native web application firewall provides for third-party managed rules to augment its functionality. That means you can protect against the threats behind the top breaches without needing to learn all the ins and out of a web application firewall. If you’re just starting out, AWS WAF Managed Rules is a good place to dip your toe into web app security and guard against the most common threats that plague applications (and business) today.
AWS WAF Managed Rules are just that – web app security rules that extend AWS WAF functionality and provide protection for any app. They’re managed, which means security experts are maintaining and updating them so you can have confidence that they’re always up to date and defending against the latest threats. It’s security as a service, in the cloud, for any app.
To protect your apps against three of the most common threats – bots, known vulnerabilities, and hacking – there are three different rules you need to consider deploying right now. Consider carefully, though, because you can only choose one (that’s 1) managed rule at a time.
OWASP Top Ten
The OWASP Top Ten are well known by developers, DevOps, and security professionals alike. You know many of their names: SQLi, XSS, command injection, No-SQLi injection, path traversal, and predictable resource. These are the top ten most common vulnerabilities that wind up giving organizations headaches (and sometimes undesirable headlines) when they’re exploited. And they often are, especially when they are found in apps that talk to data sources containing juicy consumer or corporate data.
Optimally, developers should address these in code when they are discovered. Realistically, we know it takes months for that to happen (if it does at all). That’s why a web application firewall that can address these common vulnerabilities is so valuable – because it affords instantaneous protection against exploitation. Whether as a permanent solution or stop-gap measure, it makes sense to employ a rule set that includes the OWASP Top Ten.
Common Vulnerabilities and Exposure (CVE)
The importance of protecting against known CVEs cannot be overstated.
Back in 2015, Kenna Security reported on researchconducted on a sample of 50,000 organizations with 250 million vulnerabilities and over one billion (BILLION) breach events and found two very interesting points with respect to vulnerability remediation:
- On average, it takes businesses 100-120 days to remediate vulnerabilities.
- At 40-60 days, the probability that a CVE will be exploited reaches over 90 percent.
- The gap between being likely exploited and closing a vulnerability is around 60 days.
In other words, most organizations are likely to have a CVE exploited before they get a chance to remediate. If you haven’t been paying attention, a number of *very* high profile breaches have been traced to CVEs. Like, super mega uber high profile. Consider some of the platforms and libraries with CVEs: Apache, Apache Struts, Bash, Elasticsearch, IIS, JBoss, JSP, Java, Joomla, MySQL, Node.js, PHP, PHPMyAdmin, Perl, Ruby On Rails, and WordPress. That covers most of the apps on the Internet these days.
So you definitely want to employ rules that can virtually patch your application against exploitation of CVEs as soon as they are disclosed. You should still patch them at the source (usually the platform or third-party library) but in the mean time, your app will be protected against a breach.
This remediation gap – and a dearth of security expertise – is what makes managed rules in the cloud such a good idea. Experts maintain them and ensure they’re up to date and able to protect apps against exploits, all you need to do is deploy them.
Bot Protection
More than half of all visitors to apps these days are bots. And not the good spider kind of bots crawling your site to index it and make it available through search engines. We’re talking about the seedy, Decepticon kind of bot that is searching for vulnerabilities, shoving SPAM in your communities, scraping your site, or participating in a botnet-based DDOS scheme.
Defense against bots isn’t easy. Captchas are constantly trying new methods of identifying and blocking bots, but like the seasonal flu these pesky critters just keep adapting and getting around defenses.
Still, malicious bots exhibit behaviors that can be detected and identify them as unwanted. Bot Defense rules are able to watch for those behaviors and activity that signal ungood intent and block them from interacting with your application. We’ve seen a rise in the percentage of organizations that take advantage of bot defense services over the past two quarters, and we expect this to continue given the state of things.
Deploying a bot protection rule for apps in the cloud can provide air cover that stops CVE exploitation before it happens.
Web App Firewall or Managed Rules
It’s important to note that some apps are going to need protection against all three threats. Still others will need protection against more than just bots, CVEs, and the OWASP Top Ten. Some are going to need data scrubbing and leak prevention, as well as more app-specific defenses. Schema-validation is a good example, especially when accepting data from unknown sources. L7 (application layer) DDoS is another. Protocol enforcement, too, is invaluable when protecting against TCP or HTTP-based vulnerabilities. If you need more than one (1) rule or additional protections, you’ll want to explore a full-featured Advanced WAF. And as your app grows in capabilities and customers, you’ll want to be vigilant about growing your protections for it, as well.
Regardless, managed rules are great way to get started with app protection in the cloud. They provide a solid foundation for web app security without requiring you to become a security expert yourself.
Join AWS and F5 to learn how the F5 WAF can help you safeguard your data, meet compliance regulations, and establish ongoing protection for your cloud workloads.
Join the webinar to learn:
- Key application and architecture considerations for picking the right WAF
- How F5 WAF solutions help protect your data from known and unknown threats
- How to leverage automated learning capabilities to prevent even the most sophisticated attacks on your data
Webinar Date + Time:
Wednesday, April 25, 2018 | 10:00 a.m. PT
